Old Microsoft Account credentials vulnerability remains in Windows 10
\
\
\
 \
\
\
As secure as Microsoft is touting Windows 10 to be, the remnants of older versions may still be putting new users at risk.
\
According to a research project highlighted by a ghacks.net reporter, there is a legacy bug that dates back all the way to Windows 95 that is putting Windows 8 and 10 users at risk when entering Microsoft Account credentials into some areas.
\
What happens is the following: Microsoft Edge, Internet Explorer, Outlook and other Microsoft products allow connections to local network shares. What the default settings don’t prevent on top of that is connections to remote shares.
\
An attacker could exploit this by creating a website or email with an embedded image or other content that is been loaded from a network share.
\
Microsoft products like Edge, Outlook or Internet Explorer, try to load the network share resource and send the active user’s Windows login credentials, username, and password to that network share.
\
The username is submitted in plaintext, the password as an NTLMv2 hash.
\
Perhaps the reason this vulnerability hadn’t been highlighted in versions older than Windows 8 and 10 is the fact that newer releases now encourage and use a Microsoft Account ID as the default sign in method. The move to a Microsoft Account login is unlike when users on Windows 7 and older would use the more standard local username and password when accessing Windows.
\
Ghacks.net does a deep dive into the issues that arise because of the vulnerability and also provide a link to a proof of concept web page intended to test a user’s underlying system for the vulnerability.
\
Note: Use and test the web page at your own discretion, WinBeta is not encouraging the use of the proof concept web page.
\
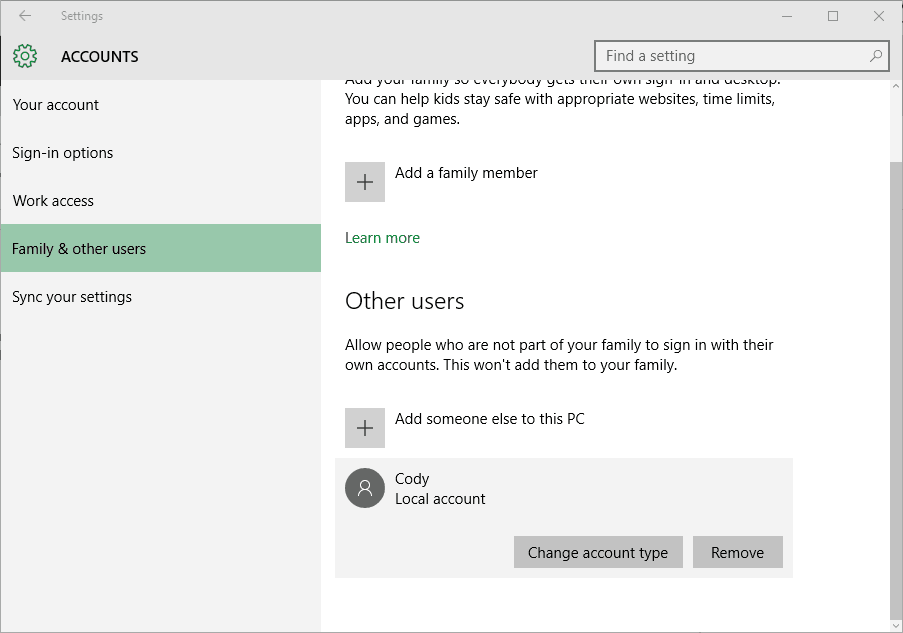
Account settings
\
Beyond pointing out the vulnerability and confirming a potential weakness in your system, the ghacks.net report also provides some pointers on avoiding or mitigating the potential damage from leaked credentials. While their initial tactic seems a bit knee-jerk and impossible for some, warning users to “use third-party products instead of Microsoft products for the time being,” the researcher who discovered the vulnerability has a bit more of a measured response regarding the use of Windows Firewall.
\
In addition to network perimeter firewalls, we, therefore, advocate for a host based hardening thanks to the Windows Firewall present on any Windows machine running at least Windows XP SP2. By enforcing egress filtering on ports 137/138/139/445 and dropping any IP packet leaving the host with a destination matching any of those ports and having a public IP as a target host, we offer a more consistent protection against those attacks.”
\
Neither proposal is ideal, but until Microsoft addresses this bug, these may be the only course of actions users affected by this vulnerability, can take, aside from using a password manager.
\
\
\
Further reading: explorer, Microsoft, Microsoft Account, Microsoft Edge, NTLMv2, Outlook, Windows 10, Windows 7, Windows 8, windows 95
\
\
\
\
\
\
\\t
\
\
\
\
\\t
\
\
\
\
 \\t
\\t \\t
\\t \\t
\\t \\t
\\t \\t
\\t \\t
\\t \\t
\\t \\t
\\t


Have you experienced or read about any other Windows 10 based vulnerabilities or bugs?