Microsoft outlines world’s ‘first hybrid war’ between Russian and Ukraine
4 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Microsoft was among the first “cyber” actors attempting to alert Ukraine to the digital threats Russia was imploring shortly before the country enacted its land invasion of the sovereign nation.
With firsthand experience and knowledge about cyberattacks preceding a physical confrontation, Microsoft released the conclusion of a report “detailing the relentless and destructive Russian cyberattacks we’ve observed in a hybrid war against Ukraine.”
Yesterday, the company posted to its Microsoft on the Issues blog, a report it commissioned that lays out the details of Russia’s seemingly sanctioned nation-state (the GRU) cyber-attacks launched in concert with kinetic military actions as well as how Microsoft sought to help protect Ukranian people and organizations during the onslaught.
Below are some details on a handful of what Microsoft believes to be upwards of 237 attacks, that also happen to align with widely reported “kinetic military operations,” listed in its detailed report.
As today’s report details, Russia’s use of cyberattacks appears to be strongly correlated and sometimes directly timed with its kinetic military operations targeting services and institutions crucial for civilians. For example, a Russian actor launched cyberattacks against a major broadcasting company on March 1st, the same day the Russian military announced its intention to destroy Ukrainian “disinformation” targets and directed a missile strike against a TV tower in Kyiv. On March 13th, during the third week of the invasion, a separate Russian actor stole data from a nuclear safety organization weeks after Russian military units began capturing nuclear power plants sparking concerns about radiation exposure and catastrophic accidents. While Russian forces besieged the city of Mariupol, Ukrainians began receiving an email from a Russian actor masquerading as a Mariupol resident, falsely accusing Ukraine’s government of “abandoning” Ukrainian citizens.
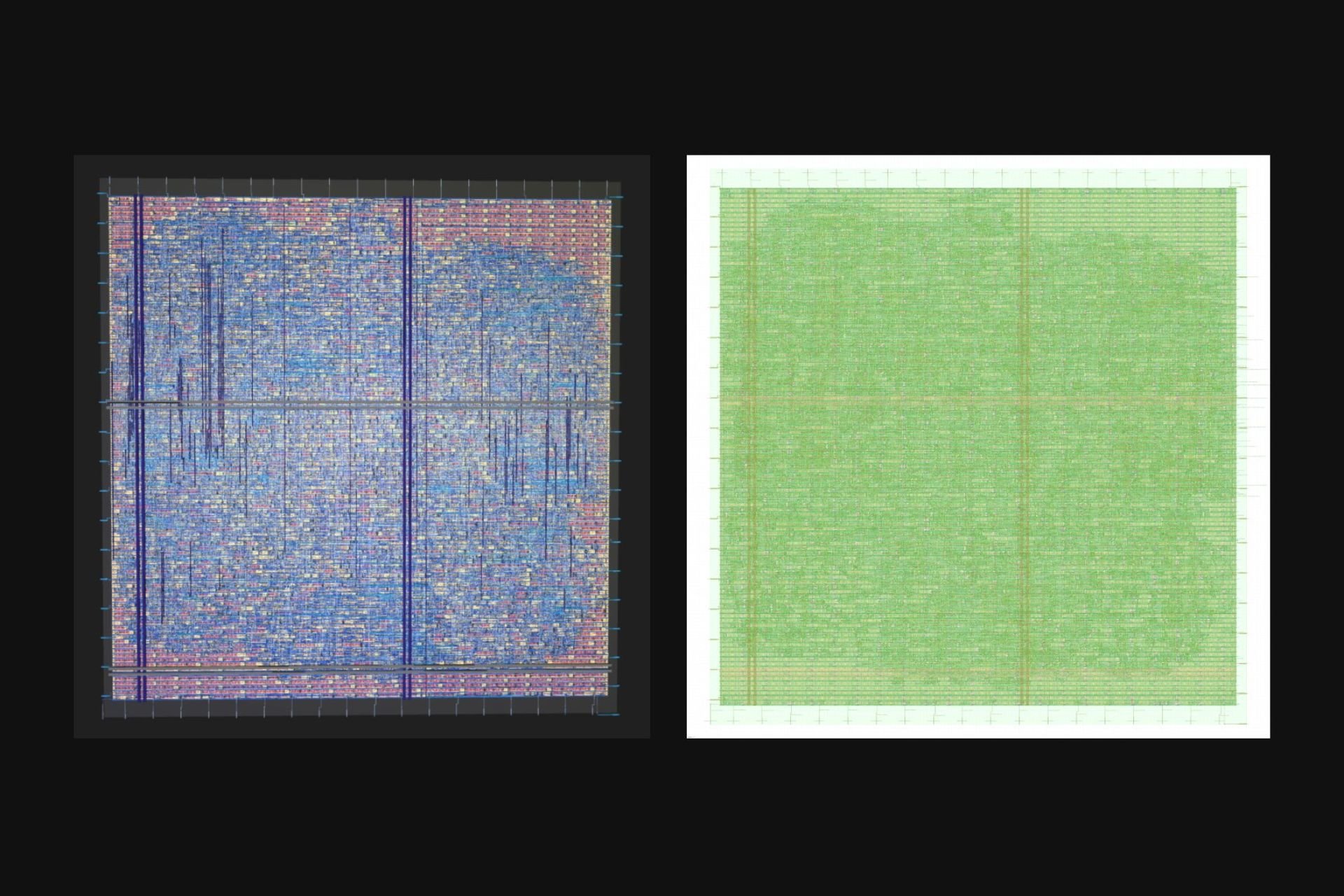
Not only does Microsoft cover more specific instances of coordinated cyberattacks, but it charts the percentage of destructive attacks concerning government, military, economic and civilian organizations or critical infrastructures as well as detailed timeline of the types of techniques used.
When Russian troops first started to move toward the border with Ukraine, we saw efforts to gain initial access to targets that could provide intelligence on Ukraine’s military and foreign partnerships. By mid-2021, Russian actors were targeting supply chain vendors in Ukraine and abroad to secure further access not only to systems in Ukraine but also NATO member states. In early 2022, when diplomatic efforts failed to de-escalate mounting tensions around Russia’s military build-up along Ukraine’s borders, Russian actors launched destructive wiper malware attacks against Ukrainian organizations with increasing intensity. Since the Russian invasion of Ukraine began, Russian cyberattacks have been deployed to support the military’s strategic and tactical objectives. It’s likely the attacks we’ve observed are only a fraction of activity targeting Ukraine.
Microsoft’s Special Report: Ukraine an Overview of Russia’s Cyberattack Activity in Ukraine is an engaging piece of immediate historical reference as per the company’s president Brad Smith puts it, marks the first publicly highlighted hybrid war.
Microsoft’s report also examines the most overt and subtle forms of cyber warfare where Smith implores the world’s nations to be on the lookout for “disinformation” campaigns which are particularly threatening to democracy around the globe.
Not all is lost by the end of the 21-page report Microsoft offers a set of recommendations that include:
- Minimizing credential theft and account abuse
- Secure internet-facing systems and remote access solutions
- Leverage anit-malware, endpoint detection, and Identity protection solutions.
- Enable investigations and recovery
- Defend against destructive attacks
- Review and implement “best practices” for defense in depth.
Microsoft vows to continue to work with Ukraine to spot, catalogue and address future Russian backed cyber aggression but also encourages liberal arts and computer majors to switch class focus for a bit to better identify the political, socio-economic, historical and engineering aspects to future hybrid war strategies.