Microsoft identifies a second SolarWinds-like attack from Russian based hackers
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Companies are still reeling from the sophisticated large scale 2020 attack on SolarWinds who worked with 320,000 customers in over 190 countries, and it appears there is a second attempt under away.
While the actual number of customers who downloaded the “impacted version of SolarWinds’ software” was much smaller at 18,000 and even fewer than 100 who were hacked, this new threat isn’t being taken lightly.
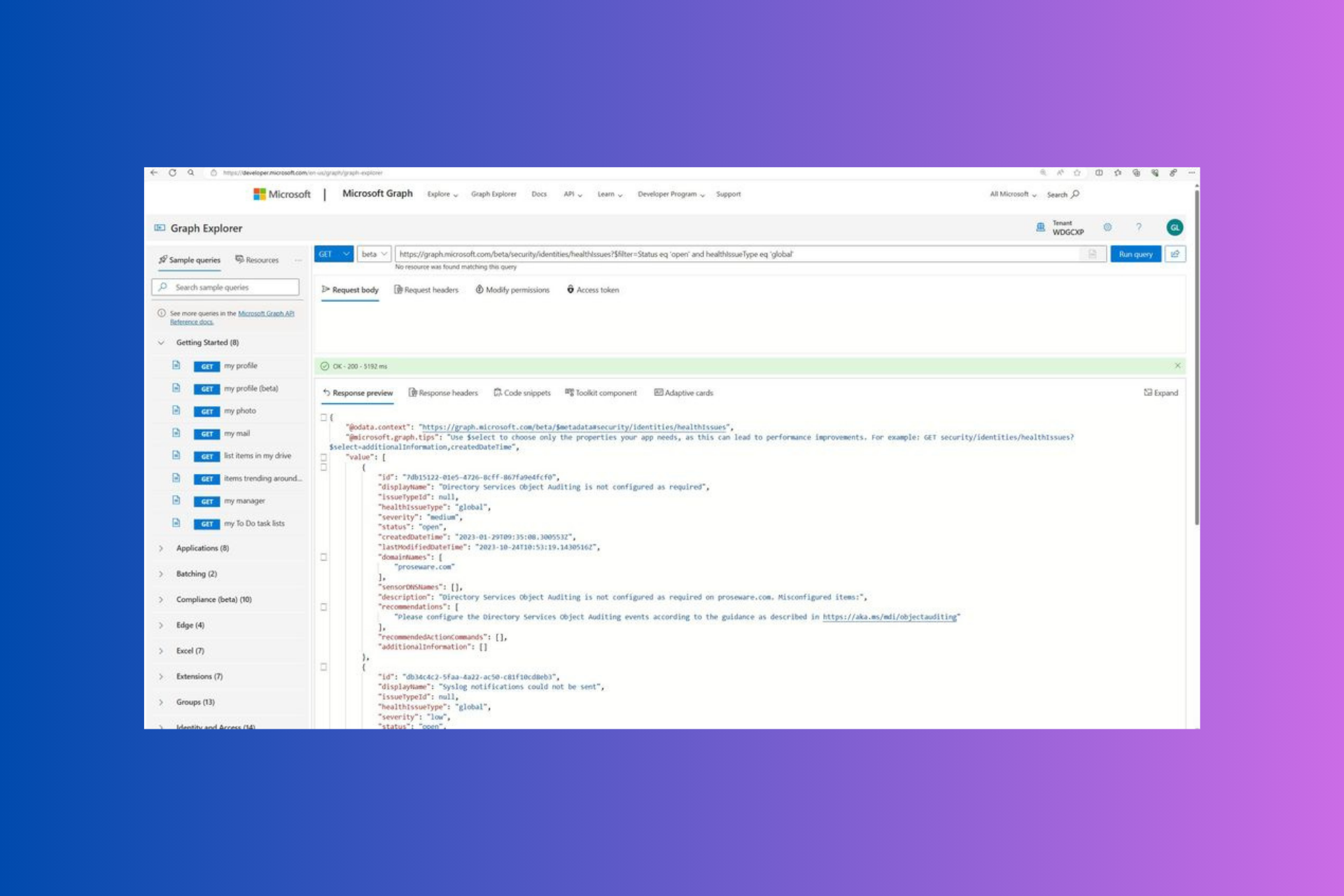
Microsoft has managed to identify a second nascent attack on the horizon that is deploying a similar Trojan-horse technique to gain direct access to cloud services used by global IT supply chains.
In a blog post authored by Microsoft’s corporate vice president of Customer Security & Trust, Tom Burt names Russian nation-state actor Nobelium as the same perpetrators of both the original SolarWinds attack and this new copycat attempt.
Nobelium has been attempting to replicate the approach it has used in past attacks by targeting organizations integral to the global IT supply chain. This time, it is attacking a different part of the supply chain: resellers and other technology service providers that customize, deploy and manage cloud services and other technologies on behalf of their customers. We believe Nobelium ultimately hopes to piggyback on any direct access that resellers may have to their customers’ IT systems and more easily impersonate an organization’s trusted technology partner to gain access to their downstream customers.
Microsoft has been keeping an eye on Nobelium since May of this year and alerting its vulnerable partners and customers which has been more than 140 resellers and service technology providers.
Sadly, Microsoft believes of the 140, at least 14 have been seriously compromised by the new attack. On the plus side, Microsoft also believes it’s caught Nobelium in the preliminary stages despite an increase in activity during the summer.
Similar to SolarWinds, Nobelium is looking to weaponize a long-term strategy of surveillance on potential Russian targets in the future, according to Microsoft.
The attacks we’ve observed in the recent campaign against resellers and service providers have not attempted to exploit any flaw or vulnerability in software but rather used well-known techniques, like password spray and phishing, to steal legitimate credentials and gain privileged access. We have learned enough about these new attacks, which began as early as May this year, that we can now provide actionable information which can be used to defend against this new approach.
Microsoft notes Nobelium isn’t the only nation-state attempting to gain illegal access to resellers IT supply chains, but it is among the most aggressive at the moment.
Microsoft is collaborating with authorities and the security community in US and European government agencies to coordinate and execute counter measures.