Amazon Web Services has introduced a managed deployment of OpenClaw on Amazon Lightsail, allowing users to launch the viral AI agent with a single setup instead of managing a complicated self-hosted installation. The new blueprint targets developers and businesses that struggled with installing OpenClaw manually on cloud servers and configuring the required security and access controls.
According to an AWS blog post, the Lightsail deployment arrives with Amazon Bedrock already configured as the default AI provider, using the Claude Sonnet 4.6 model. The system also automates IAM role creation through a CloudShell script, which removes several technical steps that usually require DevOps knowledge.
Once the instance starts running, users pair their browser through SSH credentials and then access the assistant through messaging platforms such as WhatsApp, Telegram, Slack, Discord, or a web chat interface.
Rapid growth and security concerns
OpenClaw has seen explosive adoption since early 2026. The project reached 100,000 GitHub stars within weeks of going viral and now exceeds 250,000 stars. The software began as Clawdbot in November 2025, created by developer Peter Steinberger, and later rebranded before settling on the OpenClaw name.
At the same time, security researchers have raised serious warnings. A vulnerability tracked as CVE-2026-25253 enables remote code execution through WebSocket token theft in older versions of the platform. Investigations by security firms discovered tens of thousands of internet-exposed instances, many of which store credentials for AI services such as Claude, OpenAI, and Google AI.
How the Lightsail setup works
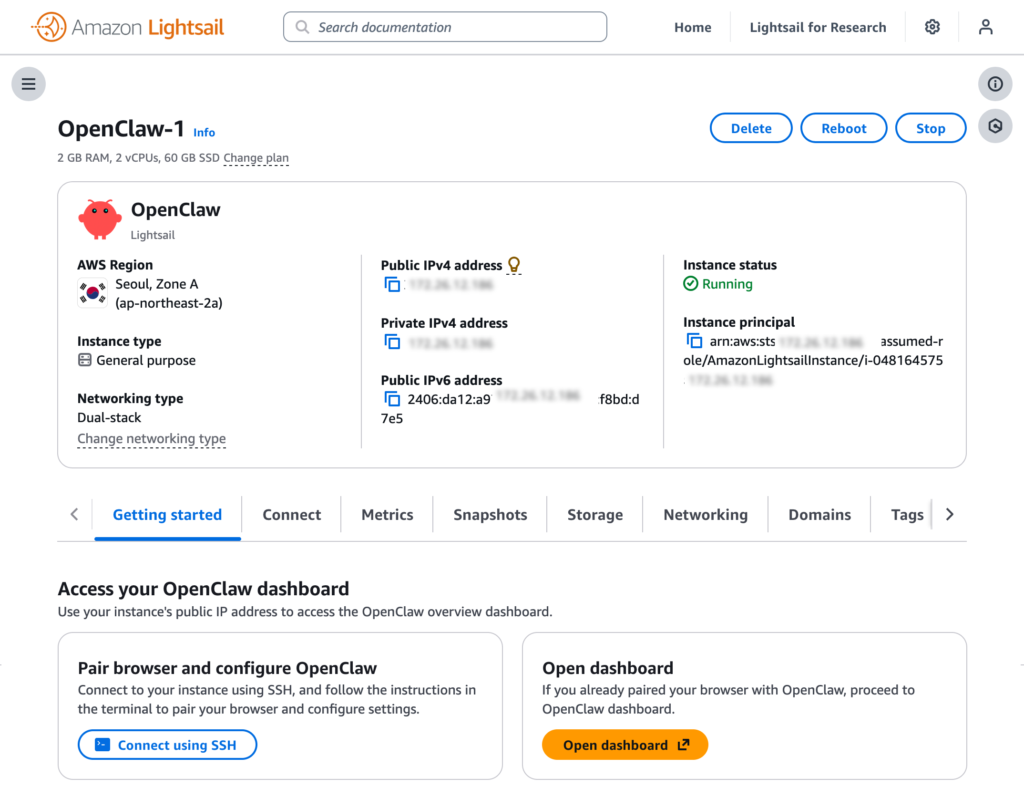
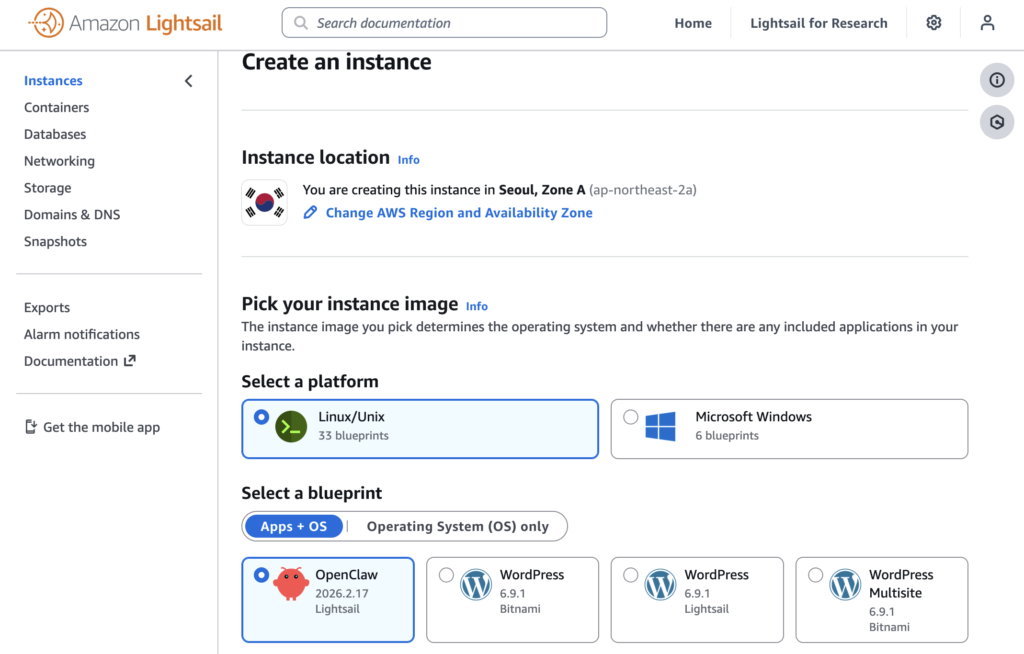
The Lightsail blueprint simplifies the process of launching the agent. Users open the Lightsail console, create an instance, select the OpenClaw blueprint, and choose a plan with at least 4 GB of memory. After the instance starts, they connect through an SSH terminal to obtain the dashboard link and authentication token.
The assistant then runs with Amazon Bedrock as its AI backend, and users can send commands directly through the OpenClaw dashboard or messaging apps linked to the system.
Security and cost considerations
AWS documentation warns that OpenClaw requires careful configuration. Administrators should avoid exposing the gateway to the public internet, rotate authentication tokens regularly, and store credentials in environment files instead of configuration files.
Running the service also involves several cost factors. Users pay for the Lightsail instance, Bedrock token usage for each message processed by the assistant, and possible software fees if they choose third-party models distributed through AWS Marketplace.
The OpenClaw Lightsail deployment is now available across all AWS commercial regions that support Amazon Lightsail.