NVIDIA’s gaming GPUs are now part of a more serious security conversation after new research showed that Rowhammer attacks can move beyond regular system memory and target GDDR memory inside certain graphics cards, opening the door to full system compromise in the right conditions.
That matters because GPUs no longer handle only games and creative work, and they now sit at the center of AI workloads, shared cloud systems, and high-performance computing setups where one successful attack can have much wider consequences than most consumers realize.
According to Ars Technica, researchers have now demonstrated multiple GPU-focused Rowhammer attacks against NVIDIA’s Ampere generation, including the GeForce RTX 3060 and RTX 6000 class cards, showing that a flaw once mostly tied to CPU memory can now cross into GPU memory and then reach the host system itself.
The headline here is simple: under the right setup, an attacker can start from unprivileged code on the GPU and work toward arbitrary memory access, privilege escalation, and even a root shell on the host machine.
Research Importance
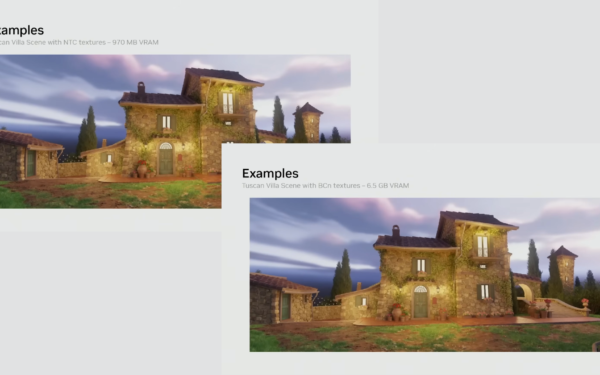
Rowhammer has been around for more than a decade, but this latest work pushes it into much more relevant territory for modern systems because it shows that GDDR memory can suffer bit flips severe enough to corrupt GPU page tables and break the normal separation between safe and unsafe memory regions.
Once attackers gain read and write access to GPU memory, they can abuse those corrupted mappings to reach CPU memory as well, which turns a graphics card issue into a full platform security problem.
“By corrupting GPU page tables, an unprivileged CUDA kernel can gain arbitrary GPU memory read/write, and then chain that capability into CPU-side escalation by exploiting newly discovered memory-safety bugs in the NVIDIA driver. The result is system-wide compromise up to a root shell, without disabling IOMMU, unlike contemporary works, making GPUBreach a more potent threat.” – Researchers behind GPUBreach, via Ars Technica
That “system-wide compromise” line is what stands out most here, especially because one of the newer attacks, GPUBreach, reportedly works even when IOMMU is enabled, which removes one of the easier defenses that earlier research relied on.
The other two attacks, GDDRHammer and GeForge, also show how far this area has moved, with researchers reporting far higher bit flip counts and practical paths to host privilege escalation.
Should gamers panic?
Right now, the real-world risk for average gamers still looks limited because there are no known cases of these attacks being used in the wild, and the research focuses on complex proof-of-concept exploits rather than mass consumer attacks.
At the same time, this is still bad news for NVIDIA because it proves that GPU memory is no longer outside the Rowhammer conversation, and that shared GPU systems in enterprise and cloud environments face a more meaningful threat than many people assumed.
For now, the known vulnerable cards named in this research are Ampere models such as the RTX 3060 and RTX 6000, while mitigations like enabling IOMMU or ECC can reduce exposure, though neither comes without tradeoffs and neither solves every version of the problem. That leaves NVIDIA users with an uncomfortable but clear takeaway: your GPU can still be great at gaming, but new Rowhammer research shows it can also become a path to handing attackers far more of your system than it ever should.